Vulnerability Intelligence
Better Automation to Outpace IT Exploits
Monitoring only tells you what you already know — threat actors use AI to discover and exploit more vulnerabilities faster. You need a smarter way to tackle vulnerabilities, too.
Cyber Resilience Lags IT Exploits
The odds of your modern network being disrupted by breaches are increasing. Learn how BackBox builds resilience by keeping network devices in a known and trusted state — all the time.
0%
of network vulnerabilities remain unpatched for over 1 year
Network Operations and Network Security Survey: What's Ahead for Automation, 2023
0%
of breaches resulted from a known and unaddressed vulnerability
Verizon Data Breach Investigations Report, 2024
200-400%
annual growth
of CVEs over the last 10 years
VuInCheck: State of Exploitation - A Peek into the Last Decade of Vulnerability Exploitation, 2024
Keep Your Network Safe
Use dynamic inventory, risk data, and scoring to help prioritize and perform device OS updates for the maximum impact on network security.
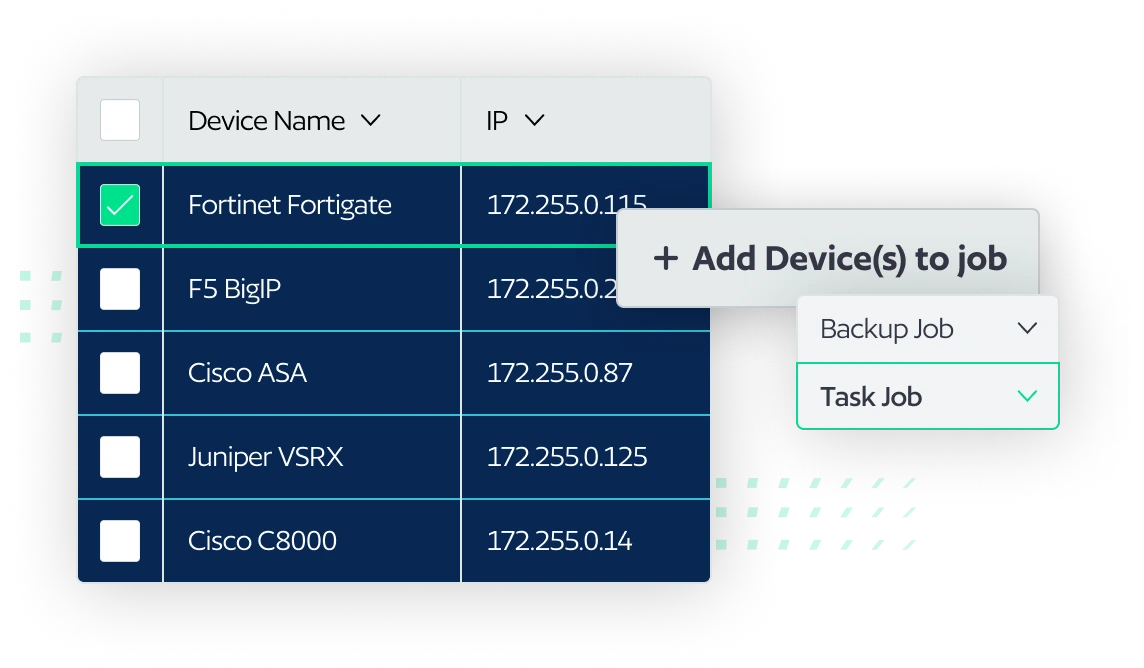
Discovery and Mapping
BackBox models your network's configuration inventory – on-prem and cloud-managed – and maps it against a threat intelligence feed using CVEs to assess the threat level.
Risk Level and Analytics
Risk level, update recommendations, and end-of-life information are used to suggest automations for addressing vulnerabilities that help prioritize device patching based on network risk.
Close Loop Between Identification & Remediation
Ensure a seamless process for tracking, scoring, and remediating vulnerabilities, with automation to fix identified vulnerabilities with minimal effort.
Remediation Prioritized by Risk Analysis
Risk analysis data helps create consensus and provides a complete picture of the priority of vulnerability patching, while the pre-built automations make deploying updates easier.
CVE Mitigation
Search device configuration files for specific vulnerable configurations to determine the relevance of any given CVE. If a vulnerability is found, it can be mitigated using automation.
Closed-loop Vulnerability Remediation with BackBox
Watch our video walkthrough or download the solution brief to learn more about how you can use BackBox to secure modern networks.
Trusted By
Over 100,000 networks worldwide choose BackBox
Our Customers Can't Stop Talking About Us
“BackBox is the ultimate toolkit for network engineers. It’s packed with tons of awesome tools for everything from finding vulnerabilities to fixing security breaches.”
“With BackBox, bi-weekly patching takes only one hour, compared to at least 35 hours to do manually.”
“BackBox is a seamless tool for managing your configuration backup and CVEs with its Network Vulnerability Management module. It’s a centralized point of configuration backup.”
“We automated our Check Point patching process to run from BackBox, so we don’t need to do it manually, as well as configuration changes on multiple devices using scripts from BackBox.”
“BackBox automates network patching, starting from pre- and post-validation to running the entire software upgrade process.”
Dive Deeper With Expert Guidance
5 Ways BackBox Helps Organizations with the EU Cyber Resilience Act
Learn how BackBox can help meet EU Cyber Resilience Act (CRA) requirements and offer valuable tools to keep the network safe.
Network Security Automation: Securing the Dynamic Enterprise at Scale
Understand exactly what network security automation is, its benefits, and implementation best practices.
Buyer’s Guide for Network Cyber Resilience Solutions
Choosing the right automation solution for your network can be challenging. We can help identify key factors to consider.
FAQS
Frequently Asked Questions About Vulnerability Intelligence
BackBox automatically discovers devices and maintains information about them, including the manufacturer, type, version, and firmware. This means you will always know the status of your devices and can easily identify which ones need patching or updates. BackBox provides insights based on Common Vulnerabilities and Exposures (CVEs) as well as information from your device vendors, websites, and other sources.
Take the next step
Cyber resilience is a continuous journey. No matter where you are, we’ll help you take the next step.