Solutions
Network Vulnerability Management Automation
Track, Score, and Remediate Vulnerabilities with BackBox NVM.
Are you certain that your network is safe from the latest vulnerabilities?
Does your vulnerability management solution only go as far as tracking CVEs without enabling action to be taken to eliminate vulnerabilities?
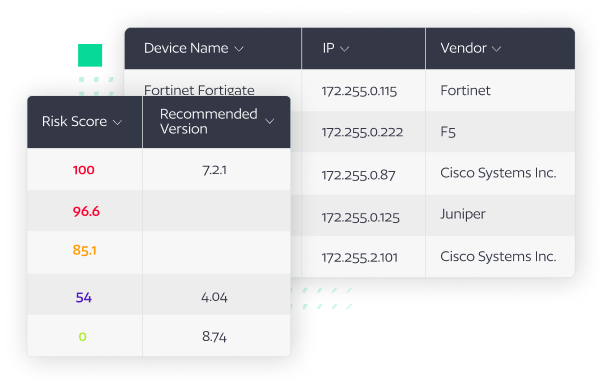
BackBox Network Vulnerability Manager (NVM) maps your dynamic inventory to a threat and vulnerability intelligence feed and uses CVEs and other security information to determine your threat level, represented as a risk score. The risk score is then used to prioritize vulnerability remediation and ensure that your time is spent in the most effective way possible to keep your network safe.
Where other vulnerability management tools present information, only BackBox automates remediation whether it means patching configurations temporarily or updating a device’s OS to implement a permanent fix.
Keep YOUR network safe
Tracking vulnerabilities and mapping them to YOUR inventory is essential to managing your network security posture and keeping your network up and running without compromise.
Understand your vulnerability state
Beyond tracking CVEs, NVM includes rich data about the vulnerabilities as well as the ability to map vulnerabilities to configuration-specific details in your devices.
Take action
Simplify updates and vulnerability mitigation with automation.
Solution overview
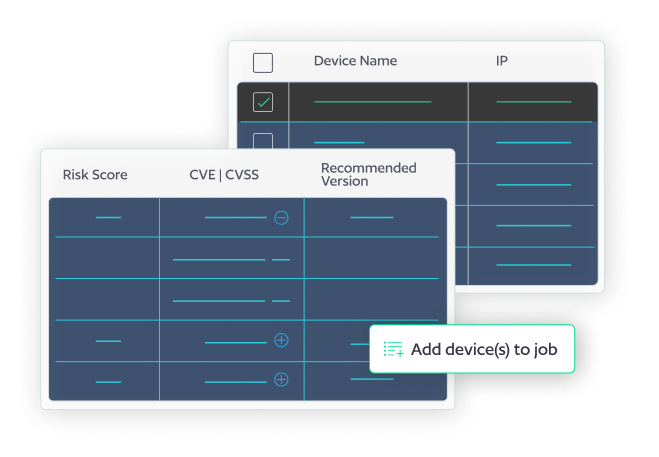
With BackBox Network Vulnerability Manager you can track the vulnerability state of
your network and take action to eliminate vulnerabilities.

Discovery and Mapping
Starting with device discovery, BackBox models the configuration inventory of your network. The inventory is mapped against a threat and vulnerability intelligence feed that uses CVEs and other security information to determine the threat level against your specific inventory.
Risk Scoring
Risk level, recommended updates and patches, product end-of-life information, and more is then used to provided recommended automations to remediate the discovered vulnerabilities and allow network engineers to prioritize device patching based on actual risk to their network.
Vulnerability Remediation
Network Vulnerability Manager is purpose-built for network teams to easily discover vulnerabilities in their network, prioritize CVEs according to their unique risk profile, and take remediation action, no matter the network complexity.
“Unpatched software is a top three access route for hackers and patching, says the UK’s National Cyber Security Centre (NCSC) “remains the single most important thing you can do to secure your technology.””
Key Features
Score your inventory
Grading your actual inventory with a risk assessment that goes beyond simply mapping CVEs to devices delivers a device risk score. Your risk score is impacted by the number of CVEs on a device and their severity, whether those CVEs are known to be actively exploited, and if the device is internet-facing.
Discount CVEs that don’t apply
Fine tune your risk score by marking irrelevant CVEs as mitigated. Searching through device configurations makes it easy to know if a CVE applies to your specific configurations, and if it doesn’t, you can recalculate the risk score so that your team is able to focus their efforts where it really matters.
Remediate vulnerabilities
BackBox takes the complexity out of the patching process while giving administrators the tools to automate the remediation of vulnerabilities. Where others provide information, only BackBox provides the tools to take action and eliminate vulnerabilities.
Why BackBox?
Whether or not you have a fully articulated network automation strategy, every day you face an onslaught of repetitive but critical tasks that, if neglected, put the network at risk. BackBox is here to reliably automate that operational work so you have confidence in the outcomes and can focus on more forward-looking projects.
Vulnerability Remediation
Maximize network-level cyber resiliency and save time with automated vulnerability remediation, restoring a trusted state with one-click backups, freeing your team to innovate and reducing tedious CVE tracking.
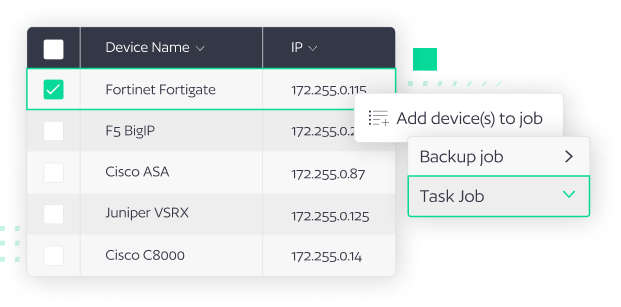
Configuration Compliance
Unlock configuration compliance at scale with no-code automations, over 3,000 pre-built tasks, and auto-remediation, saving time, and delivering cyber resiliency across your entire network estate.
Explore other solutions
NCM